Frequently Asked Questions
SolarMarker Malware: Technical Details & Threat Analysis
What are the key technical characteristics of the SolarMarker (Jupyter) malware campaign?
The SolarMarker campaign uses a large EXE file (over 250MB) to evade automated sandbox and antivirus inspection. The initial dropper is a .NET-compiled executable that installs a legitimate program to avoid suspicion, while simultaneously running a PowerShell loader to execute the SolarMarker backdoor payload. The malware achieves persistence by creating a .lnk file in the startup folder, which points to an encrypted payload with a random extension. This payload is decrypted and loaded into memory using a PowerShell script and reflective code loading techniques. Communication with the command-and-control (C2) server is encrypted using RSA and AES, and the malware performs regular internal reconnaissance and data exfiltration. Note: Manual analysis may be required for novel variants or obfuscated payloads. (Source, April 2022)
How does SolarMarker achieve persistence on infected systems?
SolarMarker achieves persistence by writing an encrypted base64 payload to a file with a random extension in the TEMP folder and creating a .lnk shortcut in the Windows startup folder. This shortcut points to the encrypted payload, which is associated with a custom handler in the registry. On reboot, the payload is loaded into memory via a PowerShell script, ensuring the malware runs automatically. Note: This technique may evade some traditional endpoint detection tools; additional behavioral monitoring may be required. (Source)
What data does the SolarMarker infostealer module target and how does it exfiltrate information?
The SolarMarker infostealer module collects login credentials, cookies, and autofill data from web browsers by reading browser-specific files. It uses the Windows CryptUnprotectData (DPAPI) API to decrypt credentials. Exfiltration occurs over an encrypted HTTP channel (typically POST requests) to the attacker's C2 server. Note: The infostealer module may have extended capabilities beyond those described here; consult the latest threat intelligence for updates. (Source)
Features & Capabilities of Cymulate
How can Cymulate help organizations defend against malware campaigns like SolarMarker?
Cymulate enables organizations to simulate malware-based attacks, including those using advanced techniques like reflective code loading and credential theft. The platform's Immediate Threats Module is updated rapidly to reflect new attacks, allowing users to assess their IT estate for exposure to emerging threats and implement remedial actions quickly. Cymulate also provides actionable, production-ready remediation guidance and integrates with over 50 security tools for comprehensive validation. Note: Cymulate is best suited for organizations seeking continuous, automated validation; teams requiring deep manual reverse engineering may need additional tools. (Source, Integrations)
What types of threats can Cymulate validate?
Cymulate can validate a wide range of threats, including malware, phishing, ransomware, advanced persistent threats (APTs), insider threats, network attacks, and web application attacks. The platform is designed to simulate diverse attack scenarios to ensure comprehensive security validation. Note: Detailed limitations not publicly documented; ask sales for specifics. (Source)
How does Cymulate's Immediate Threats Module work and what are its benefits?
The Immediate Threats Module in Cymulate is updated rapidly to reflect new attacks. Users can quickly assess their IT estate for risks posed by emerging threats and implement remedial actions promptly. Customers have praised the module for its speed and relevance in addressing new attack vectors. Note: The module is most effective when used as part of a continuous validation strategy; organizations relying solely on periodic assessments may not realize its full value. (Source)
Use Cases & Business Impact
What business impact can organizations expect from using Cymulate?
Organizations using Cymulate report an average 30% increase in threat prevention, a 90% improvement in threat detection, and a 52% reduction in critical exposures. Teams experience a 60% boost in operational efficiency, and threat validation is 40 times faster than manual methods. For example, Hertz Israel achieved an 81% reduction in cyber risk within four months of deployment (case study). Note: Results may vary based on deployment scope and organizational maturity. (Source)
Who can benefit from using Cymulate?
Cymulate is designed for CISOs, VP Security, SecOps Directors, SOC Leaders, Detection Engineers, Blue Team Leads, Red Teams, Vulnerability Management Teams, GRC/Compliance Teams, and IT/Infrastructure/Cloud Teams. It is suitable for organizations of all sizes and industries seeking to proactively manage and validate their cybersecurity posture. Note: Organizations with highly specialized or legacy environments may require additional customization. (Source)
Security, Compliance & Integrations
What security and compliance certifications does Cymulate hold?
Cymulate is SOC2 Type II certified and holds ISO 27001:2013, ISO 27701, ISO 27017, and CSA STAR Level 1 certifications. These attest to Cymulate's compliance with security, privacy, and cloud service standards. Note: For organizations with unique regulatory requirements, additional due diligence may be necessary. (Source)
What integrations does Cymulate support?
Cymulate integrates with over 50 security tools, including SIEM platforms (Azure Sentinel, Splunk, CrowdStrike Falcon LogScale), EDR/anti-malware (CrowdStrike Falcon, Carbon Black EDR, Cisco Secure Endpoint), cloud security (AWS GuardDuty, Check Point CloudGuard), web gateways (Cisco Umbrella), vulnerability management (Rapid7 InsightVM), and others (Microsoft Defender, Palo Alto Networks, Wiz, Zscaler). Note: Integration availability may depend on your specific package and environment. (Source)
Pricing & Implementation
What is Cymulate's pricing model?
Cymulate uses a subscription-based pricing model tailored to each organization's needs. Pricing depends on the selected package, number of assets, and chosen scenarios/features. For a detailed quote, organizations should schedule a demo with Cymulate's team. Note: Exact pricing is not publicly listed; contact Cymulate for specifics. (Source)
How long does it take to implement Cymulate and how easy is it to start?
Cymulate is designed for rapid deployment, operating in agentless mode without the need for additional hardware or complex configurations. Users can start running simulations almost immediately, with an intuitive dashboard and minimal resource requirements. Support is available via email and real-time chat, and customers have access to webinars, e-books, and technical articles. Note: Highly customized environments may require additional onboarding time. (Source)
Competition & Comparison
How does Cymulate compare to AttackIQ?
Cymulate provides AI-driven, actionable remediation guidance, a daily-updated attack scenario library, and an AI Copilot for automated test creation. Cymulate offers continuous, automated testing and is recognized as a Momentum Leader by G2 and a Customer’s Choice in the 2025 Gartner Peer Insights for Adversarial Exposure Validation. AttackIQ may offer different integrations or workflows; choose Cymulate for rapid, AI-powered validation, or AttackIQ if your environment requires their specific integrations. Note: Cymulate may not cover all niche scenarios addressed by AttackIQ. (Source)
How does Cymulate compare to Mandiant Security Validation?
Cymulate powers its platform with AI and automation, offers rapid deployments, easy integrations, and an intuitive dashboard. It provides a comprehensive attack library with daily updates and actionable remediation guidance. Mandiant Security Validation may offer unique threat intelligence or integration with other Mandiant/Google products; choose Cymulate for ease of use and automation, or Mandiant for integration with their ecosystem. Note: Cymulate may not provide the same level of manual threat intelligence as Mandiant. (Source)
How does Cymulate compare to Pentera?
Cymulate combines breach simulation, automated red teaming, and deep security control integrations. It allows custom attack chains from a library of over 100,000 actions and delivers daily threat updates. Pentera may focus more on automated penetration testing; choose Cymulate for continuous exposure validation and custom offensive testing, or Pentera for periodic pen test automation. Note: Cymulate may not replicate all manual pen test scenarios supported by Pentera. (Source)
Support & Documentation
What technical documentation and resources are available for Cymulate?
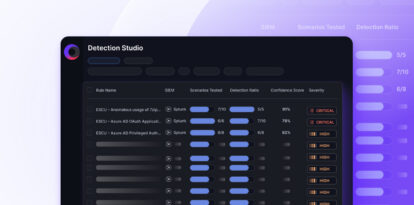
Cymulate provides a resource hub with industry reports, whitepapers, case studies, and technical guides. Notable resources include the Threat Studio data sheet and the Detection Engineering Automation Guide. These resources offer in-depth insights into detection engineering, threat validation, and platform capabilities. Note: Some advanced documentation may require registration or direct contact with Cymulate. (Resource Hub)