Continuously Identify, Scan & Map Internal & External Assets to Assess Risk
Map potential attack paths across networks, cloud platforms, and
identity systems – including Active Directory services
Identify vulnerabilities and exploitable assets that create exposure risk
Emulate reconnaissance and probing methods of threat actors to map
the external attack surface – including the dark web for organization-
specific threats
Benefits of Cymulate Attack Surface Management

Comprehensive Visibility
Visualize gaps & weaknesses in the entire infrastructure, on-prem & in the cloud

Unified Attack Path Mapping & Analysis
Put information into context for a better view of strengths and gaps

Mitigation Prioritization
Target remediation to close gaps to critical systems, resources, and data

Risk Scoring
Track and trend risk scores for continuous improvement and benchmark against peers
Capabilities
Internal & External
Asset Discovery
- Scan on-prem, cloud, and hybrid infrastructures
- Identify visible systems, applications, interfaces, and
domains - Automate scans without survey-based auditing
- Re-scan regularly to catch new issues
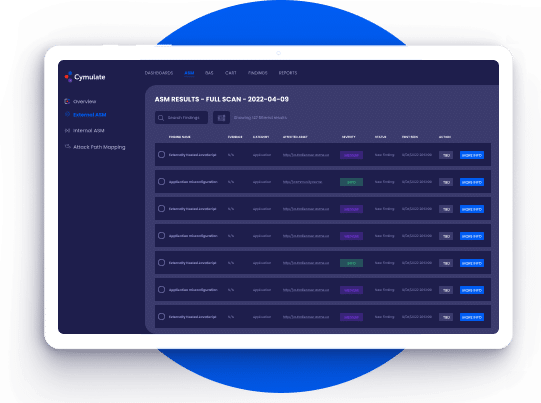
Vulnerability, Misconfiguration
& Dark Web Scanning
- Probe frameworks, libraries, services, and applications
- Identify CVEs, phishing domains, potential data
exposure, and more - Find misconfigurations, over-provisioning, and other problems
- Scan domains, subdomains, IPs, ports, clouds, configurations,
devices, and privileges - Search the dark web for sensitive information and indicators of
data leaks and cyber attacks
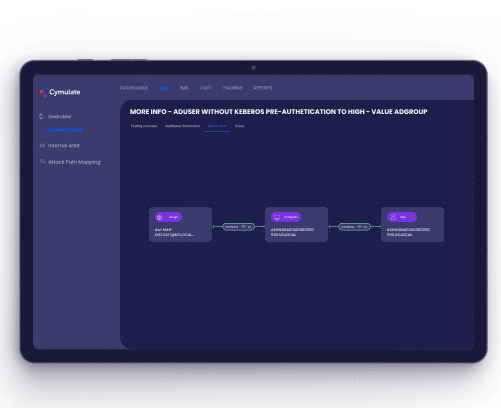
Unified Attack Path
Mapping and Analysis
- Map viable attack paths across networks, cloud,
identity systems, and Active Directory services - Quickly identify security gaps and map how
threat actors can exploit them - Prioritize high-risk attack paths by degree of
exploitability
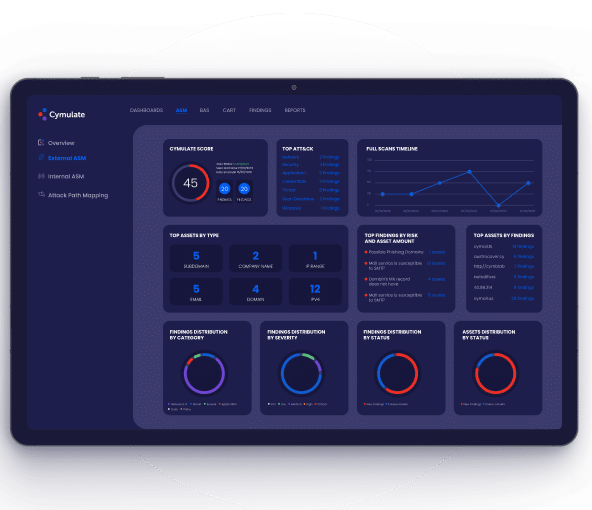
Actionable Reporting
- Ongoing reporting for drift detection and remediation
guidance - Graphically map attack information
- At-a-glance view of top attacks, assets, and findings
- Deep technical detail for drill-down
- Findings mapped to the MITRE ATT&CK® tactics,
techniques, and procedures
The Cymulate Exposure Management and Security Validation Platform
Cymulate Attack Surface Management is available both as a standalone SaaS offering and as an
integrated offering within the Cymulate Exposure Management and Security Validation Platform.
Environments
Cymulate provides extensive coverage of on-prem and cloud environments to identify vulnerabilities and misconfigurations with attack path maps for each security gap.

On-premises
- Internal systems
- Legacy applications
- User networks

Cloud
- IaaS
- Containers
- Serverless / APIs

Hybrid
- Remote Workers
- Shared Services
- Cloud Storage
Cymulate Continuous Automated Red Teaming
Scalable
Scalable
Automated testing to reduce repetitive, labor-intensive manual tasks and increase productivity
Extensive
Extensive
Network pen testing, phishing awareness, and full kill-chain campaigns
Comprehensive
Comprehensive
Supports automated testing for vulnerability validation, what-if scenarios, targeted, and custom testing
Easy
Easy
Deploys with ease, customizable, and runs ongoing non-disruptive assessments
Backed By the Industry


Cymulate Recognized as Top Innovation Leader
Cymulate Named Innovation Leader in the Frost & Sullivan’s Frost Radar™️
Related Resources
Attack Surface Management FAQs
ASM is the ongoing process of discovering points within data systems that could be used to attack the organization (servers, applications, services, cloud components, workstations, etc.) and defining and implementing remediation strategies to address gaps.
Cymulate ASM is designed to meet the needs of businesses of all sizes and industries. The platform provides organizations with comprehensive visibility into their digital assets and potential vulnerabilities. Cymulate ASM uses automated scanning to identify potential attack vectors within on-prem, hybrid, and cloud environments and provides real-time insights and recommendations for mitigating risk. This helps businesses proactively manage their attack surface and reduce their exposure to cyber threats.
Cymulate ASM can identify vulnerabilities and misconfigurations in internal and external systems, such as cloud-based systems, web applications, vulnerable third-party software, remote access systems, and email systems. It can also discover shadow IT, unmanaged assets, and access control issues that could create attack vectors for cybercriminals.
Traditional EASM platforms focus only on external threats, while Cymulate ASM offers a more comprehensive and efficient approach to attack surface management with both cloud and on-premises assets. The platform goes beyond vulnerability scanning to discover misconfigurations and attack surfaces, aiding in prioritizing vulnerabilities and gaps that threat actors can use for more effective and efficient remediation programs. Additionally, Cymulate ASM’s unified attack pathing for both cloud and on-premises provide an additional layer of understanding the probability of different security breaches.
The external attack surface of an organization includes sensitive or proprietary information stolen from the organizations that ends up for sale or exchange on the dark web, which potentially leads to further attacks or breaches. Both the dark web and publicly available information contribute to an organization’s external attack surface by providing intelligence about the organization that attackers can use to target systems, accounts, and individuals.
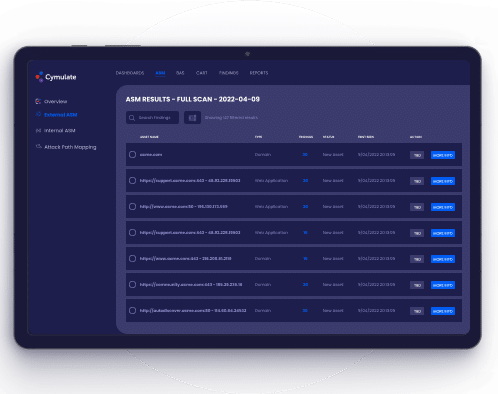
Cymulate ASM includes asset discovery scans and monthly comprehensive scans. Asset Discovery Scans are weekly, non-intrusive scans that identify assets within an organization’s IT infrastructure. The scan helps organizations gain visibility into their assets, including any unauthorized devices or software. The monthly Full Scans conducted provide a comprehensive assessment of an organization’s IT infrastructure. It identifies all assets within the infrastructure and performs vulnerability scanning on domains, subdomains, applications, and infrastructure. The full scan detects vulnerabilities, web misconfigurations, open ports, and more. The results of the full scan include a detailed report of discovered assets, vulnerability findings, and a risk score to help organizations prioritize their mitigation efforts effectively.
No, Cymulate ASM is designed to assess and monitor an organization’s external digital footprint—the part of its network that is visible from the outside, such as exposed web servers, applications, and services. This assessment is done from the perspective of an external attacker looking for publicly accessible systems and vulnerabilities that could be exploited.