Cymulate For Mergers and Acquisitions
Due diligence during any merger or acquisition process is vital to the successful conclusion of the deal. While priority is often given to financial operations, cybersecurity is just as vital to analyze and review during and after the M&A process.
Cymulate provides methods to accurately assess the cybersecurity posture of both participants, and aids in the planning of the upcoming unification of systems as the merger progresses.
Mergers & Acquisitions Challenges
Due diligence of cybersecurity resiliency brings unique challenges.
Difficult to Verify
Difficult to Verify
Survey-based auditing can show many aspects of each participant’s systems; but may cause issues to be overlooked until it is too late.
Partial Coverage
Partial Coverage
Traditional testing methods are point-in-time, and may have been performed months or even years before the merger process begins.
Limited to Assets and Applications
Limited to Assets and Applications
Inventories may not expose security issues caused by the interconnection of systems before, during, and after merger operations.
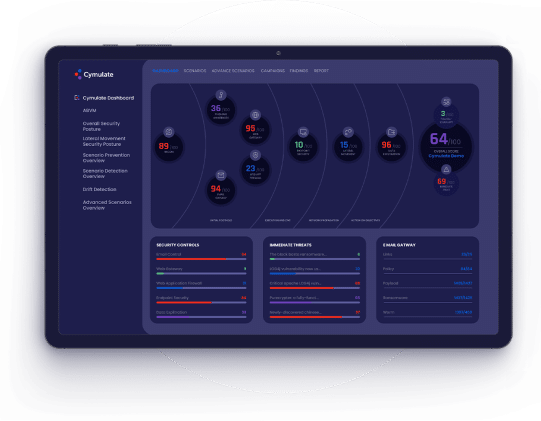
Cymulate Assessment
Before, During, and After
M&A
Running assessments on a target acquisition infrastructure
provides a birds-eye view of their exposure posture.
During the initial unification of systems, knowledge of gaps –
provided by Cymulate assessments – can allow both sides to adapt.
When unification proceeds, the best tools and methods of each
company can be kept and propagated to the combined organization.
Running a Cybersecurity Due Diligence with Cymulate
The Benefits of Cymulate M&A Assessment

Straightforward
Requires minimal skill set to obtain comprehensive evaluation

Preemptive
Prevents post-acquisition discovery of costly cybersecurity flaws

Automated
Can be run rapidly with minimal resources and provide fast and comprehensive results

Learn More About Cymulate
Mergers and Acquisitions
Overview of the Cymulate Mergers and Acquisitions solution.
Backed By the Industry
In Security it’s almost impossible to estimate a Return of Investment or even a cost-saving number, but it’s crystal clear that we have optimized our resources by using Cymulate.
Daniel Puente, CISO of Wolter Kluwer







“Cymulate has been helping me to evaluate my security posture against behavior based as well zero day threats.”
– IT Security & Risk Management Associate

“Technical capabilities provided are outstanding, customer service is highly responsive and product mgmt. is flexible in supporting us with our requests.”
– Security Operations Analyst

“The Cymulate BAS is delivering excellent outcomes, contributing significantly to enhancing my security effectiveness.”
– IT Security & Risk Management Associate

“My experience with the platform was exceptional. It delivers on its promises with easy navigation, effective mitigation steps, and top-notch after sales support.”
– Chief Risk Manager

“Always willing to help offering training sessions and encourage use of the product’s additional available features.”
– Senior Software Engineer

“I believe that Cymulate brings a vision of risks, vulnerabilities and actions that we are unable to pay attention to in our work day.”
– Security Operations Specialist

“The range and breadth of attack scenarios, potential targets and how well each tool integrates is really excellent.”
– Penetration Tester

“We had an excellent experience with Cymulate, from product deployment to while using the platform.”
– Senior Cybersecurity Engineer

“Awesome customer support and techniques used by Cymulate to identify security gaps.”
– IT Security & Risk Management