Frequently Asked Questions
Product Overview & Purpose
What is Cymulate's Email Gateway Validation solution?
Cymulate's Email Gateway Validation is an automated security validation solution that tests and optimizes your secure email gateway against the latest email-borne threats. It uses breach and attack simulations to assess the efficacy of your email defenses, helping you identify and remediate vulnerabilities before attackers can exploit them. [Source]
What is the primary purpose of Cymulate's Email Gateway Validation?
The primary purpose of Cymulate's Email Gateway Validation is to proactively validate your email security controls, identify gaps and weaknesses, and optimize your defenses against phishing, ransomware, and other email-based threats. It enables organizations to continuously measure and improve their email gateway security posture. [Source]
How does Cymulate's Email Gateway Validation work?
Cymulate's Email Gateway Validation works by sending over 10,000 production-safe test emails that simulate the latest malicious links, attachments, executable payloads, and more. It assesses your email gateway's ability to detect and block these threats, providing detailed findings, risk scores, and mitigation guidance. [Source]
What types of threats does Cymulate's Email Gateway Validation simulate?
The solution simulates a wide range of email-borne threats, including malicious links and attachments, executable payloads, dummy code execution, true file type detection, and tests of email attachment policies. [Source]
What are the main benefits of using Cymulate's Email Gateway Validation?
The main benefits include automated security validation, identification of gaps and weaknesses, optimization of security controls, and reduction of exposure risk to phishing and other email-based threats. [Source]
Features & Capabilities
What features does Cymulate's Email Gateway Validation offer?
Key features include fully automated assessment, breadth of attack simulations (over 10,000 test emails), detailed findings and reporting, mitigation guidance, and continuous measurement of email gateway security controls. [Source]
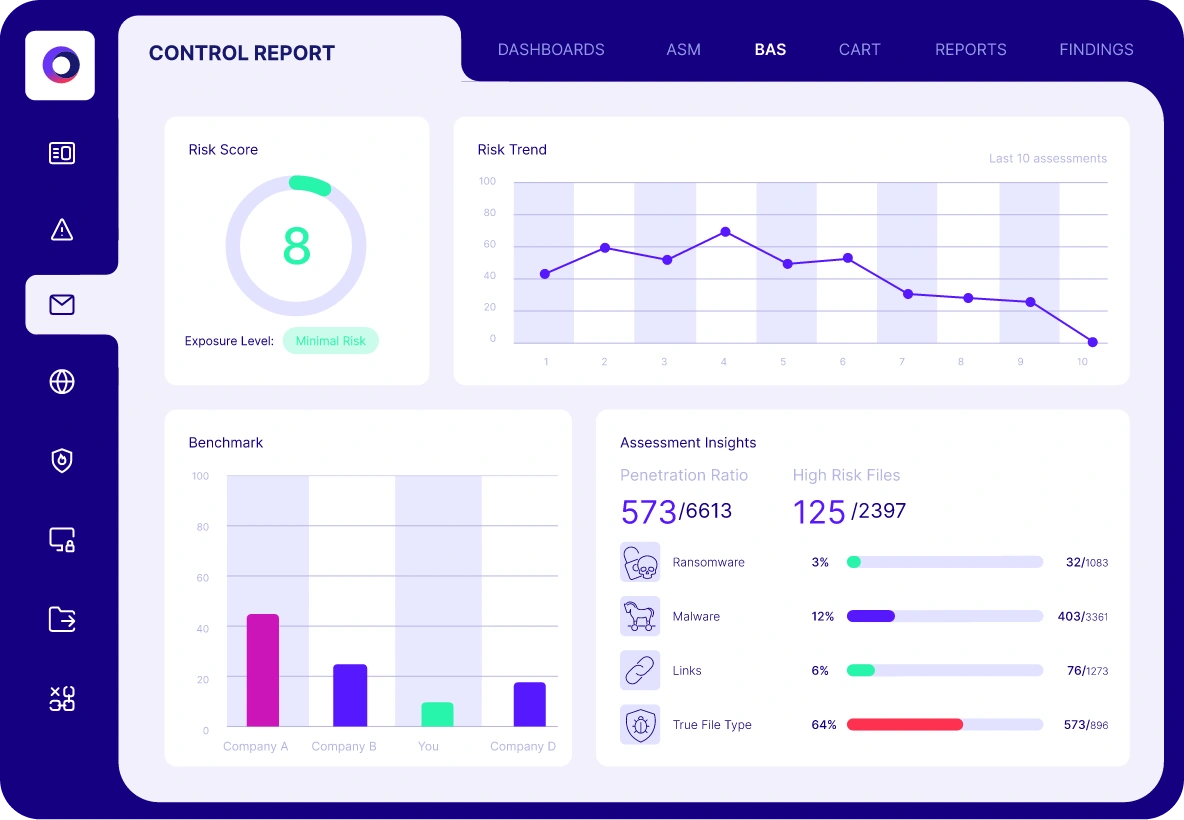
Does Cymulate's Email Gateway Validation provide detailed reports?
Yes, the solution provides deep insight into your email risk score, penetration ratio, attack type breakdown, high-risk files, and actionable mitigation guidance to optimize your email security investment. [Source]
How does Cymulate help optimize email gateway security controls?
Cymulate provides mitigation guidance based on assessment results, enabling you to configure and tune your email gateway controls to better detect and block emails containing malicious links and payloads. [Source]
What specific areas does Cymulate's Email Gateway Assessment cover?
The assessment covers malicious links and attachments, executable payloads, dummy code execution, true file type detection, and email attachment policies. [Source]
Does Cymulate provide information on best practices for email gateway security validation?
Yes, Cymulate provides information on security validation best practices for email gateway controls in their blog post. Read the blog post.
Are there resources available to learn more about Email Gateway Validation?
Yes, Cymulate offers a solution brief, a blog post on validation best practices, and a whitepaper on relieving the stress from email-based threats. These resources are available on the Cymulate website. [Source]
How does Cymulate's Email Gateway Validation help reduce exposure risk?
By continuously measuring and improving your email gateway security controls, Cymulate helps reduce the risk of phishing attacks and other email-based threats. [Source]
Results & Metrics
What measurable results can organizations expect from Cymulate's Email Gateway Validation?
Organizations have seen a 91% improvement in malicious file detection post-mitigation, an 89% reduction in email gateway risk score within two weeks, and a 50% improvement in the prevention of known attack techniques. [Source]
How quickly can organizations remediate email gateway flaws with Cymulate's guidance?
In a documented case, a customer was able to remediate an email gateway flaw within one hour using Cymulate's guidance. [Source]
What specific exposure did Cymulate's Email Gateway Assessment uncover for a banking customer?
The assessment revealed that the customer's gateway blocked emails with singular attachments but failed to block emails containing a zip file with an executable (.exe), exposing a significant vulnerability. [Source]
Use Cases & Target Audience
Who can benefit from Cymulate's Email Gateway Validation?
Organizations of all sizes and industries that rely on email for business communication can benefit, especially those seeking to proactively defend against phishing, ransomware, and other email-borne threats. [Source]
Is Cymulate's Email Gateway Validation suitable for regulated industries?
Yes, Cymulate's solution is suitable for regulated industries such as finance, healthcare, and others, as it helps validate compliance with security policies and regulatory requirements. [Source]
What roles within an organization benefit most from Cymulate's Email Gateway Validation?
CISOs, security leaders, SecOps teams, and IT security professionals benefit most, as the solution provides actionable insights, quantifiable metrics, and continuous validation to support strategic and operational security goals. [Source]
Implementation & Ease of Use
How easy is it to implement Cymulate's Email Gateway Validation?
Cymulate is designed for quick and easy implementation, operating in agentless mode with no need for additional hardware or complex configurations. Customers can start running simulations almost immediately after deployment. [Source]
What feedback have customers given about the ease of use of Cymulate?
Customers consistently praise Cymulate for its intuitive, user-friendly interface and ease of use. For example, a Cybersecurity Manager stated, "Cymulate is easy to implement and use—all you need to do is click a few buttons, and you receive a lot of practical insights into how you can improve your security posture." [Source]
What support resources are available for Cymulate users?
Cymulate provides comprehensive support, including email and chat support, a knowledge base with technical articles and videos, webinars, e-books, and an AI chatbot for quick answers and guidance. [Source]
Security & Compliance
What security and compliance certifications does Cymulate hold?
Cymulate holds several key certifications, including SOC2 Type II, ISO 27001:2013, ISO 27701, ISO 27017, and CSA STAR Level 1, demonstrating adherence to industry-leading security and privacy standards. [Source]
How does Cymulate ensure data security and privacy?
Cymulate ensures data security through encryption for data in transit (TLS 1.2+) and at rest (AES-256), secure AWS-hosted data centers, a tested disaster recovery plan, and compliance with GDPR. [Source]
What application security measures does Cymulate use?
The platform is developed using a strict Secure Development Lifecycle (SDLC), including secure code training, continuous vulnerability scanning, and annual third-party penetration tests. [Source]
Is Cymulate GDPR compliant?
Yes, Cymulate incorporates data protection by design and has a dedicated privacy and security team, including a Data Protection Officer (DPO) and Chief Information Security Officer (CISO), ensuring GDPR compliance. [Source]
Pricing & Plans
What is Cymulate's pricing model?
Cymulate operates on a subscription-based pricing model tailored to each organization's requirements. Pricing depends on the chosen package, number of assets, and scenarios selected. For a detailed quote, you can schedule a demo with the Cymulate team. [Source]
Integrations & Compatibility
What integrations does Cymulate offer for Email Gateway Validation?
Cymulate integrates with a wide range of security technologies, including email gateways, endpoint security, cloud security, and vulnerability management solutions. For a complete list, visit the Cymulate Partnerships and Integrations page. [Source]
Customer Proof & Success Stories
What do customers say about Cymulate's Email Gateway Validation?
Customers across industries praise Cymulate for its ease of use, actionable insights, and effectiveness in continuous validation. For example, a Banking Industry Information Risk Officer said, "We need a tool to measure malware attack related risks for Endpoint, Email and Web gateways and to mitigate them. We get it, it's easy to run tests ad-hoc or regularly, we know the risks and we can verify how our cyber defense is effective." [Source]
Are there case studies demonstrating the impact of Cymulate's Email Gateway Validation?
Yes, Cymulate features case studies such as Hertz Israel reducing cyber risk by 81% in four months and other organizations improving detection and remediation with Cymulate's solutions. [Source]