Endpoint Security Validation
Test and optimize your endpoint defenses against malicious
files and behaviors.
Sophisticated phishing and ransomware attacks continue to rise as adversaries target endpoint devices.
Cyber attacks
are malware free
Source: Crowdstrike
Attacks bypass AV
and EDR controls
Source: Morphisec
Average cost of an
endpoint data breach
Source: IBM
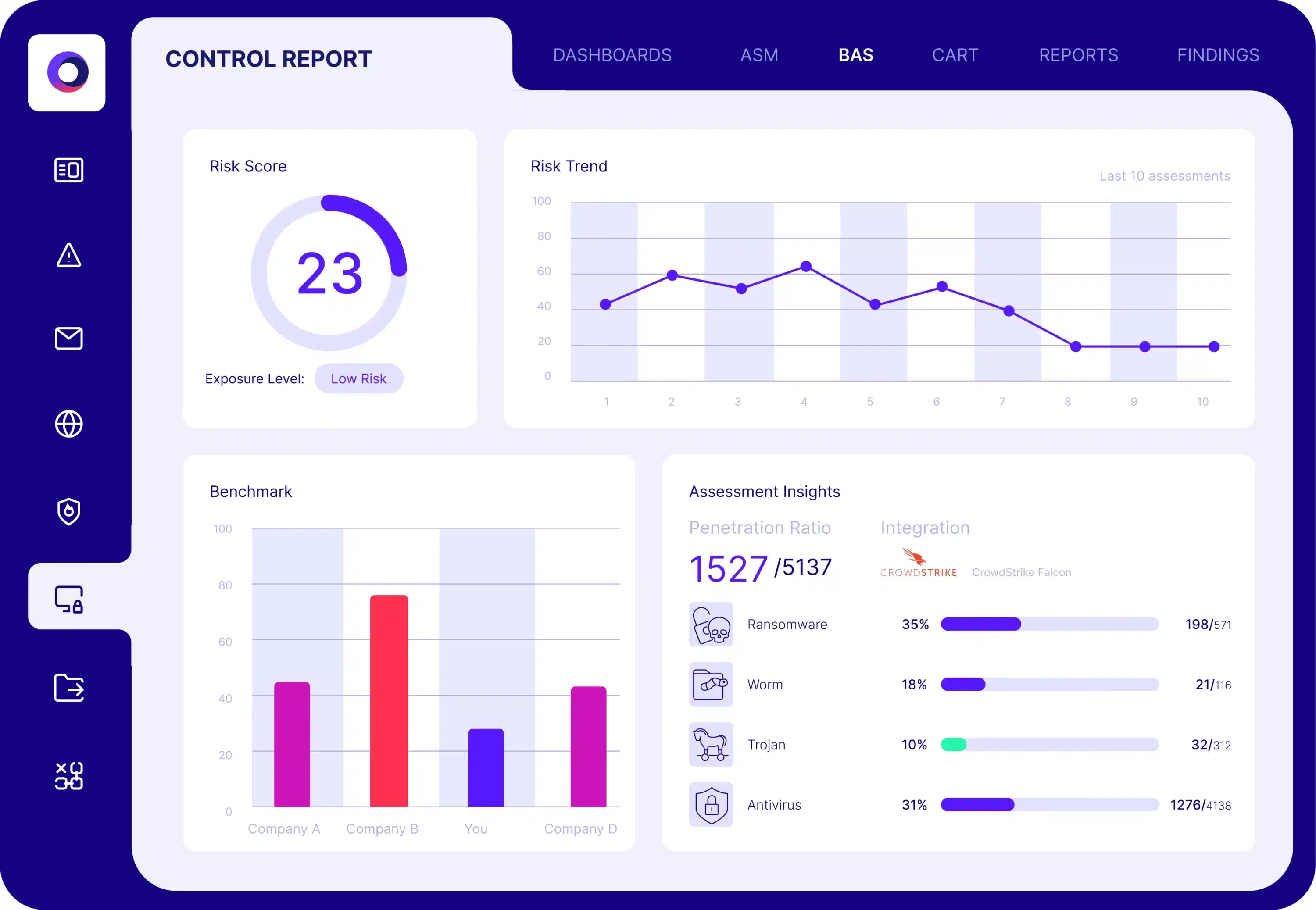
Endpoint Security Assessment
Cymulate uses breach and attack simulation to assess the efficacy of your endpoint defenses. The automated security validation simulates a wide range of known malicious file samples and behaviors that validate the effectiveness of your endpoint security controls including:
- Known malicious file samples
- Malicious behaviors
- Ransomware, worms, trojans
- Rootkits
- DLL side-loading
- Code injection
Solution Results
60%
Increase in team
efficiency
25%
Reduction in manual
SecOps tasks
70%
Reduction in vulnerabilities
between pen tests
Solution Benefits
Continuous control validation
Identify gaps and weaknesses
Optimize security controls
Reduce exposure risk
What our customers say about us
Organizations across all industries choose Cymulate for automated cybersecurity validation, proactively confirming that defenses are robust and reliable – before an attack occurs.