The Challenge: Evaluating Security Products
You have decided that you need to either replace or augment your current security stack with new technology. There are many alternative offerings and sifting through 3rd party reports and data sheets is not helping. You want to evaluate the alternative offerings quickly, comprehensively and in a consistent manner to choose the best solution for your use cases and requirements. Furthermore, you are required to demonstrate return on your security investment, demonstrating improved protection after the acquisition and implementation.
The Solution
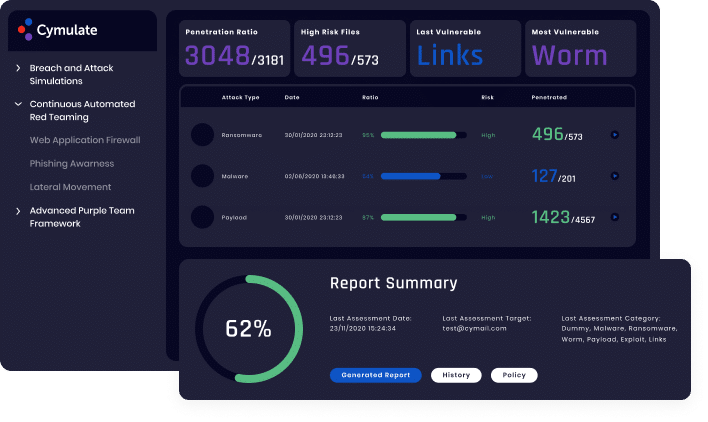
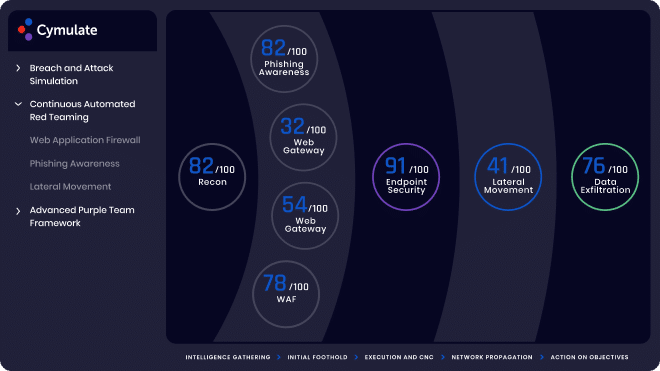
By using Cymulate security validation you can subject different vendor offerings to the same broad spectrum of attacks and evaluate their efficacy. You can use out-of-the-box assessments in addition to crafting assessments that validate specific use cases. Using the MITRE ATT&CK framework as a reference Cymulate will provide comparable results of the different solutions. Cymulate also provides a risk score of the aggregate results based on standards-based frameworks, including NIST risk assessment (Special Publication 800-30), CVSS v3 and DREAD. These quantified metrics enable you to baseline existing security performance and build a transparent business case and expected return on the new security investment (ROSI). Now you can run a technical evaluation quickly, comprehensively and in a consistent manner to select the best fit for your organization.
Benefits

Enhanced Process

Comparative Baselining

Customizable Scored Assessment
Learn More
Simply Know
Control and assure the security posture
of your organization with the most
comprehensive Continuous Security
Validation platform.
More Solutions
Learn how Cymulate makes it easy to keep all angles of your company safe and secure.

Security Control Validation
Comprehensive SIEM/SOC and IR assessment with many scenarios permutations
SIEM Validation
Optimized SIEM Performance
with enhance detection and
reduced false positives
Mergers and Acquisitions
Comprehensive M&A security posture analysis of planned acquisitions
Operationalizing Threat Intelligence
Continuously updated emerging threats resilience evaluation

Cloud Security Validation
Continuous cloud security control validation and mitigation optimization

Attack Surface Management
Continuous Security Validation with 360°
exposure visibility, comprehensive
threat vector identification
and resilience scoring

Attack Based Vulnerability Prioritization
Data backed optimized mitigation prioritization

SOC and SOAR Validation
End-to-end threat detection and IR playbook optimization through comprehensive automated continuous security validation