Continuously Validate Security Control
Effectiveness with Production-Safe
Threat Assessments
Cymulate BAS solutions safely conduct threat activities, tactics, techniques, and procedures in production environments to validate security control effectiveness.
Realistic testing of security architecture reduces exposure risk
Continuous, automated validation of security operations processes, efficiency and efficacy
Justify or protect budgets by showing control efficacy and coverage gaps
Measure, track, and report cybersecurity KPIs and overall threat exposure
Cymulate Breach and Attack Simulation Portfolio
Cymulate BAS Scenarios
- Out-of-the-box Test Scenarios
- Security Control Validation
- Immediate Threats Intelligence
- Full Kill-Chain Scenarios
- MITRE & NIST Mappings
Security Control Validation
Security is built upon a layered defense that needs continuous testing to assess if controls are working effectively. Cymulate Breach and Attack Simulation tests for detection and alerting on threats to confirm that controls are functioning correctly or if threats can evade them. Each vector is scored independently and aggregated for an overall risk score based on industry-standard frameworks.
Improve
Security
Posture

Realistic Control Testing

Offensive testing based on threat actor techniques and tactics – simulated safely

Mitigation Guidance

Clear steps to remediate, close gaps and reduce exposure

Continuous Validation

Repeat assessments to validate mitigations and identify drift

Automation

Scheduled and automated testing provides the flexibility to test on demand or upon threat updates

Risk Scoring

Track and trend risk scores for continuous improvement. Benchmark against peers

Identify Exposure to Latest Active Threats
Continuous updates with new assessments for
current active and emerging threats.
Validate Security
Architecture Against
APT Attacks
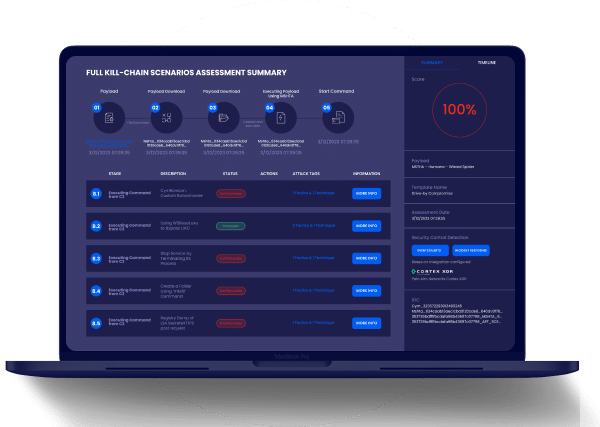
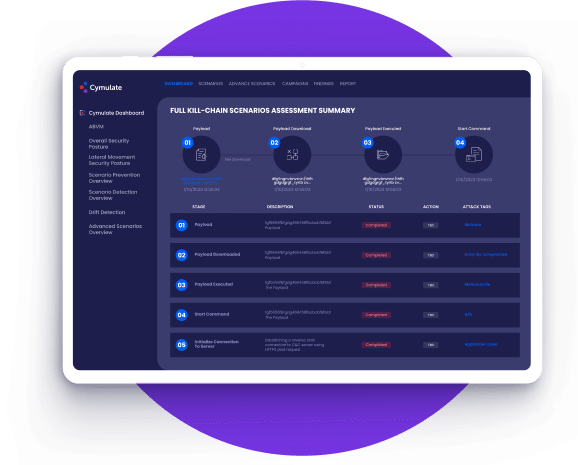
Test the full stack of cyber controls vs. simulated full
kill-chain APT attacks – from attack delivery to
exploitation and post-exploitation.
Cymulate BAS Capabilities
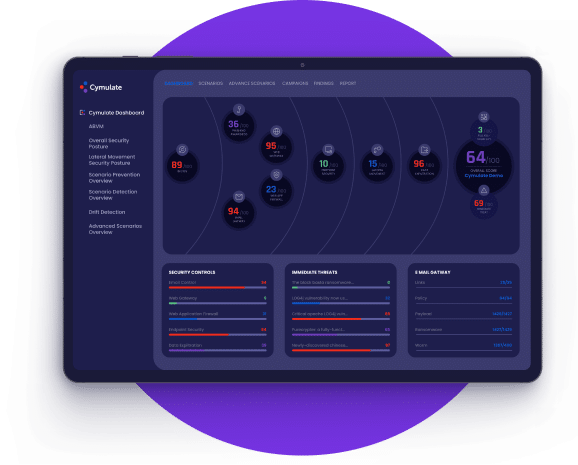
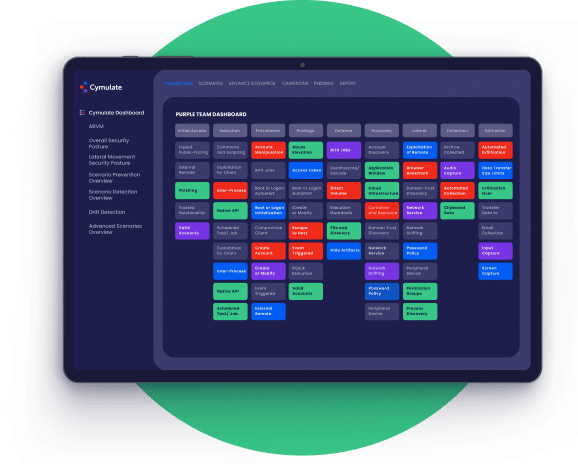
Comprehensive Dashboard
Data-driven simulations and insights into breach feasibility for
proactive risk management.
- Responsive dashboard shows security control health by
control and in aggregate - Intuitive user interface provides an easy drill down into details
- Extensive vendor integrations to maximize operational
efficiency while minimizing risk exposure - Remediation insights provide straightforward guidance
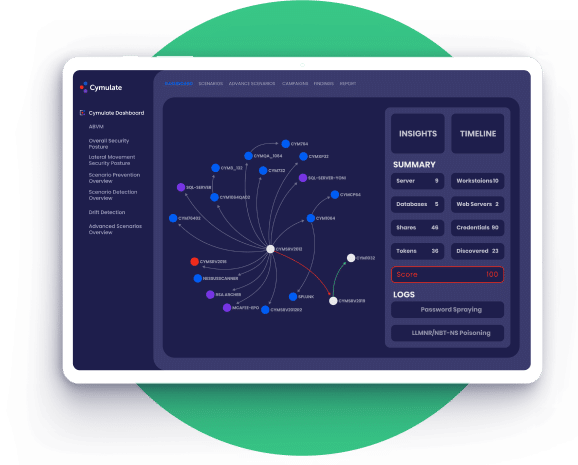
Simulation Scenarios
- Sourced from real-world attacks using known adversary
Tactics, Techniques, and Procedures (TTP’s) - Over 120,000 attack simulations provided in safe and
effective, ready-to-use broad-spectrum templates - Custom templates, attacks, binaries, and executions
available through scenarios and template building tools - Scenarios to assess across the entire Cybersecurity Kill-
Chain and with integrated support for MITRE ATT&CK®
reporting
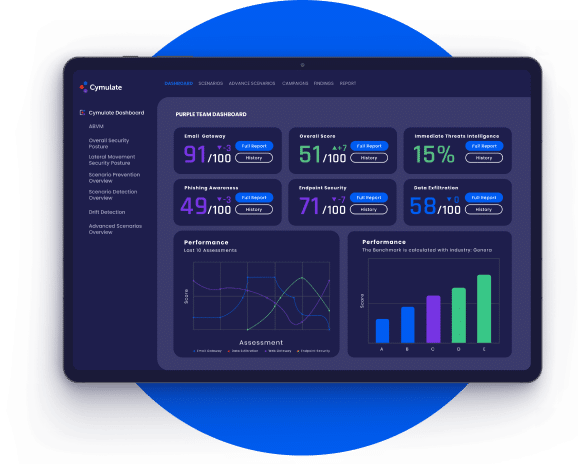
Actionable Reporting
- Reporting with risk scores, attack summaries, and
optimization insights - Increased information sharing and collaboration between
Red, Blue, and Purple Teams - Executive reporting with industry benchmarking
- Mapping to MITRE ATT&CK®
- Custom dashboards and reporting
- Investment decision support – Discover redundancies,
ineffective controls, perform product comparisons, etc.
Mitigation Guidance
- Mitigation methodologies for each discovered gap
- Multiple pathways for remediation provided
- SIGMA support for data sharing
- Integrations with EDR/XDR, SIEM, SOAR, and other tools
for correlation of data to facilitate more targeted
remediation actions
MITRE ATT&CK® Reporting
- Reports include mapping to the MITRE ATT&CK® framework
- Custom scenario components are mapped to MITRE ATT&CK®
tactics and techniques - Heatmaps show areas of strengths and gaps
Environments
The attack surface constantly changes, requiring organizations to plan for an react to these changes.
Cymulate provides extensive attack simulation and immediate threat testing across on-premises, cloud,
and hybrid infrastructure and supports a wide variety of operating systems.

On-premises
- Internal Systems
- Legacy Applications
- User Networks

Cloud
- IaaS
- Containers
- Serverless/APIs

Hybrid
- Remote Workers
- Shared Services
- Cloud Storage
Windows
- Desktop
- Servers
- Virtual

Linux
- RedHat
- Debian
- Forked Distributions

MacOS
- Intel
- Apple Silicon
- 10.13 and higher
Backed By the Industry


Cymulate Recognized as Top Innovation Leader
F&S recognized in their Frost Radar™️ Global BAS, 2022 report
Related Resources
Breach and Attack Simulation FAQs
BAS is a process that allows businesses to simulate cyber-attacks on their systems and networks to identify weaknesses in their security posture. BAS helps organizations proactively identify and address security issues before an attack occurs. It also ensures they are better prepared to defend against real-world threats.
Cymulate BAS launches attack scenarios to discover security gaps and assess the layers of an organization’s security stack. It is cloud-based, providing continuous updates that enable customers to test new threats as they emerge. Deployment is quick and easy, with assessments launched directly from the cloud and some requiring a lightweight agent that serves as a proxy, minimizing installation and maintenance efforts. Cymulate BAS Scenarios includes control validation capabilities for email gateways, web gateways, web application firewalls, endpoint security, and data exfiltration. Additional capabilities feature immediate threat assessments, full kill-chain scenarios, and advanced scenarios—a customizable open-attack framework.
Cymulate BAS provides organizations with comprehensive security control validation. The modular solution addresses a wide variety of business and technical use cases. Security professionals leverage Cymulate’s insights to prioritize and reduce cyber risk, justify investments, provide proof of security resilience to management and boards, and for compliance and regulatory programs. Additionally, companies that utilize Cymulate BAS, CART (Continuous Automated Red Teaming), and ASM (Attack Surface Management) gain visibility into the full spectrum of their organizations’ exposure and breach feasibility—with one consolidated platform.
Traditional penetration testing services typically involve a one-time assessment of an organization’s security posture. Cymulate BAS provides ongoing, continuous assessments that simulate various real-world attack scenarios on specific security controls. This allows businesses to identify and remediate vulnerabilities in real-time rather than waiting for an annual or bi-annual assessment.
Every organization, regardless of size or industry, can benefit from a BAS solution. Cybersecurity threats are prevalent across all sectors, and implementing a BAS solution can help companies identify and address weaknesses in security controls and exploitable vulnerabilities in their security infrastructure before they are exploited by attackers. It is recommended to find a consolidated platform that covers many use cases and can scale and adapt to an organization’s evolving security needs as it progresses in its cyber maturity.
Vulnerability scans list vulnerabilities found in an organization’s environment and prioritize them based on the Common Vulnerability Scoring System (CVSS) rather than the vulnerability’s exploitability in the organization’s specific environment. Cymulate BAS continuously provides organizations the visibility on how well their security controls prevent vulnerabilities from being exploited. This allows companies to create a risk-reduction action plan based on prioritization. Cymulate’s simulated and emulated attacks complement severity with exploitability and account for the effectiveness of compensating security controls in an environment.