Webinar
July 13th, 2022
Webinar: How to Prevent Production Shutdown with a Proactive Approach to Cybersecurity
Cyberattacks on the manufacturing industry have seen an increase in…

Whitepaper
July 3rd, 2022
Outsmart Ransomware with Security Controls Validation
Learn the many faces of ransomware and how to avoid…

Case Study
June 28th, 2022
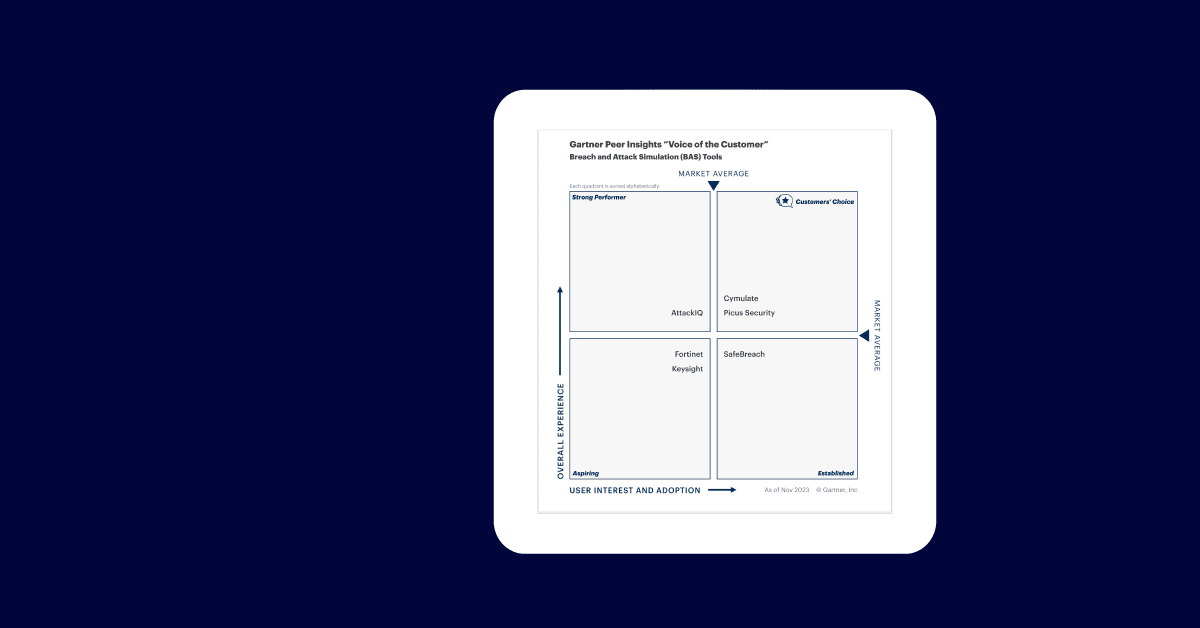
Hedge Fund Optimizes Testing Against Emerging Threats with Cymulate
Case Study For a global hedge fund with a small…

eBook
June 28th, 2022
15 Ways Cymulate Increases ROI
eBook CISOs and SOC leaders are often sorely lacking in…

Video
June 28th, 2022
Anxiety-Free Vulnerability Management with Magda Chelly
Leverage Attack Based Vulnerability Prioritization to find vulnerabilities and reduce…

Video
June 27th, 2022
THIS is What Cyber Confidence Looks Like
What does cyber confidence look like? ‣ Like reading the…

Webinar
June 22nd, 2022
Webinar – 2022 Data Breaches Study; Methods, Implications, and Prevention
Webinar In this annual report, Cymulate surveyed over 800 enterprises…

Brochure
June 22nd, 2022
Complying with NIST 800-53 Revision 5 Standards
NIST Revision 5 aims to: Improve the efficiency of conducting…

Report
June 15th, 2022
2022 Data Breaches Survey Report
Our 2022 breach survey report will help security decision-makers craft…

Podcast
May 2nd, 2022
Conti Ransomware Gang Analysis with
SimplyCyber
SimplyCyber’s Gerald Auger and Cymulate’s Director, Cyber Evangelist Dave Klein…

Webinar
April 28th, 2022
Insights for CISOs: Cybersecurity Implications of the War in Ukraine
Listen to this discussion on the cybersecurity implications of the…

Case Study
March 31st, 2022
Cymulate Empowers Government IT Security Services to Keep Defenses High
Case Study A government agency is chartered with the setting,…

Webinar
March 26th, 2022
How an Expert-led Security Optimization Program Can Reduce Risk
Webinar Are you unsure about how to integrate continuous security…

Webinar
March 24th, 2022
Making SecOps & Security Leaders More Successful
Webinar Learn the best security operations practices for measuring and…

Webinar
March 23rd, 2022
Validación continua de la seguridad en infraestructuras críticas con Agbar
Seminario Web El impacto de un ciberataque a una infraestructura…

Whitepaper
March 22nd, 2022
Are Cyber-Insurance Models Broken?
Understanding how the cyber-threat landscape affects policies and claims for…

Webinar
March 16th, 2022
Quick Wins for a BFSI CISO
Webinar External risks and internal pressures are driving FS CISOs…

Podcast
March 15th, 2022
Cyber Risk and Risk Reduction with Magda Chelly – Cymulate Cybersecurity Podcast
Dr. Magda Chelly of Responsible Cyber and Dave Klein discuss…

Podcast
March 13th, 2022
Application Security Validation for CI/CD with Tanya Janca – Cymulate Cybersecurity Podcast
Never have applications, most web-based, been more critical for the…

Video
March 6th, 2022
Cymulate Gives You Confidence
Get the confidence you need to make data-driven, intelligence-led decisions…

Podcast
March 6th, 2022
Essential Purple Teaming Management with Tracey Maleeff
To mitigate and reduce cybersecurity risks it is essential that…

Podcast
March 6th, 2022
Demystifying Zero Trust with Chuck Brooks Cymulate Cybersecurity Podcast
Zero Trust has become the framework of choice to reduce…

Webinar
February 26th, 2022
Cymulate 2021 State of Cybersecurity Effectiveness
Watch this informative webinar for an in-depth understanding of the…

Report
February 17th, 2022
IDC Report: How MSSPs Can Validate Cybersecurity Posture Continuously
MSSPs have a responsibility to validate their services for their…

Case Study
February 10th, 2022
TASE Implements a Continuous Security Validation Process
Learn how Cymulate hardened the security posture of Tel Aviv…